Cisco AnyConnect Secure Mobility Client empowers remote workers with frictionless, highly secure access to the enterprise network from any device, at any time, in any location while protecting the organization. 1300 York Avenue, Box 12 New York, NY 10065 Phone: (212) 746-4878 Fax: (212) 746-8161.
OpenConnect is a cross-platform multi-protocol SSL VPN client which supports a number of VPN protocols:
- Cisco AnyConnect (--protocol=anyconnect)
- Juniper SSL VPN (--protocol=nc)
- Pulse Connect Secure (--protocol=pulse
- Palo Alto Networks GlobalProtect SSL VPN (--protocol=gp)
- F5 Big-IP SSL VPN (--protocol=f5)
- Fortinet Fortigate SSL VPN (--protocol=fortinet)
OpenConnect is not officially supported by, or associated in any waywith Cisco Systems, Juniper Networks, Pulse Secure, Palo Alto Networks, F5,or Fortinet, or any of the companies whose protocols we may support in the future.It just happens to interoperate with their equipment. Trademarks belong totheir owners in a rather tautological and obvious fashion.
An openconnect VPN server (ocserv), which implementsan improved version of the Cisco AnyConnect protocol, has also beenwritten.
OpenConnect is released under the GNU Lesser Public License, version 2.1.
Motivation
Development of OpenConnect was started after a trial of the Cisco AnyConnectclient under Linux found it to have many deficiencies:


- Inability to use SSL certificates from a TPM or PKCS#11 smartcard, or even use a passphrase.
- Lack of support for Linux platforms other than i386.
- Lack of integration with NetworkManager on the Linux desktop.
- Lack of proper (RPM/DEB) packaging for Linux distributions.
- 'Stealth' use of libraries with dlopen(), even using the development-only symlinks such as libz.so — making it hard to properly discover the dependencies which proper packaging would have expressed
- Tempfile races allowing unprivileged users to trick it into overwriting arbitrary files, as root.
- Unable to run as an unprivileged user, which would have reduced the severity of the above bug.
- Inability to audit the source code for further such 'Security 101' bugs.
Naturally, OpenConnect addresses all of the above issues, and more.
New protocols
Adding new protocols to OpenConnect is relatively simple, andadditional protocols have been added over the years since usingOpenConnect allows a developer to concentrate on the protocol itselfand most of the boring details about platform-specific tunnel managementand IP configuration, and handling of client SSL certificates, are alreadyresolved.
If you have a protocol which you think it makes sense to support inOpenConnect, especially if you are able to help with interoperabilitytesting, please file an issuein GitLab.
Consistent multi-protocol support
Wherever possible, OpenConnect presents a uniform API and command-lineinterface to each of these VPNs. For example,openconnect --force-dpd=10will attempt dead peer detection every 10 seconds on every VPN thatsupports it, even though the actual mechanism used may be protocol-specific.Protocol-specific features and deficiencies are described on theindividual protocol pages.
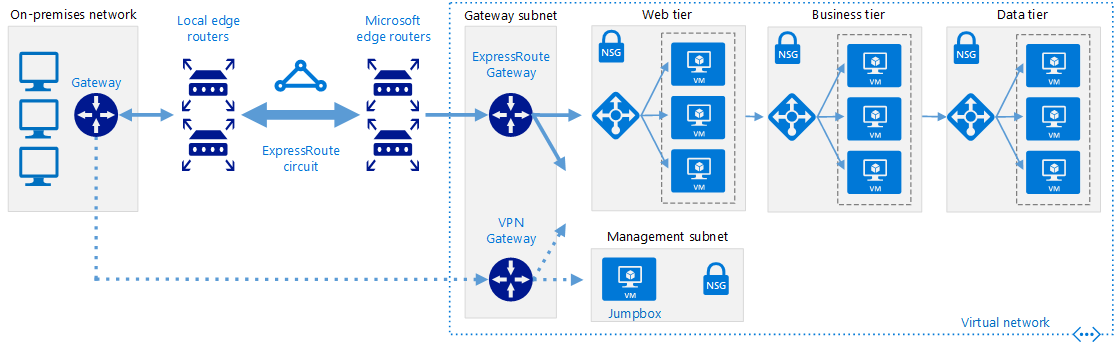
Today applications are evolving and moving to the public cloud. Amazon Web Services (AWS) offers different types of services to host these applications in the cloud. Customers are opting for hybrid cloud services because it provides the optimum architecture for application hosting and performance. This change in cloud architecture introduces a big challenge of providing a secure connection to the remote workers.
Cisco provides a comprehensive solution by offering Cisco Adaptive Security Appliance (ASAv) and Cisco Next-Generation Firewall in the AWS marketplace. These virtual appliances can integrate with the Cisco security portfolio and provides unmatched remote access VPN architecture for AWS.
Figure 1: Components of the Cisco Secure Remote Worker
- Cisco AnyConnect Secure Mobility Client:Cisco AnyConnect Secure Mobility Client empowers remote workers with frictionless, highly secure access to the enterprise network from any device, at any time, in any location while protecting the organization. It provides a consistent user experience across devices, both on and off-premises, without creating a headache for your IT teams. Simplify management with a single agent.
- Cisco Duo:Cisco Duo is a user-friendly, scalable way to keep business ahead of ever-changing security threats by implementing the Zero Trust security model. Multi-factor authentication from Duo protects the network by using a second source of validation, like a phone or token, to verify user identity before granting access. Cisco Duo is engineered to provide a simple, streamlined login experience for every remote user. As a cloud-based solution, it integrates easily with your existing technology and provides administrative, visibility, and monitoring.
- Cisco Umbrella Roaming Security Module: Cisco Umbrella Roaming Security module for Cisco AnyConnect provides always-on security on any network, anywhere, any time — both on and off your corporate VPN. The Roaming Security module enforces security at the DNS layer to block malware, phishing, and command and control callbacks over any port. Umbrella provides real-time visibility into all internet activity per hostname both on and off your network or VPN.
- Cisco Advanced Malware Protection (AMP) Enabler:Cisco AnyConnect AMP Enabler module is used as a medium for deploying Advanced Malware Protection (AMP) for Endpoints. It pushes the AMP for Endpoints software to a subset of endpoints from a server hosted locally within the enterprise and installs AMP services to its existing user base. This approach provides AnyConnect user base administrators with an additional security agent that detects potential malware threats happening in the network, removes those threats, and protects the enterprise from compromise. It saves bandwidth and time taken to download, requires no changes on the portal side, and can be done without authentication credentials being sent to the endpoint. AnyConnect AMP Enabler protects the user both on and off the network or VPN.
- Cisco Identity Services Engines (ISE):Cisco AnyConnect Secure Mobility Client offers a VPN posture module and an ISE posture module. Both provide the Cisco AnyConnect Secure Mobility Client with the ability to assess an endpoint’s compliance for things like antivirus, antispyware, and firewall software installed on the host. The administrator can then restrict network access until the endpoint is in compliance.
- Cisco Adaptive Security Appliance (Virtual Appliance):The Cisco Adaptive Security Appliance (ASA) is a security appliance that protects corporate networks and data centers. It provides users with highly secure access to data and network resources – anytime, anywhere. The remote users can use Cisco AnyConnect Secure Mobility Client on the endpoints to securely connect to the resources hosted in the Data Center or the Cloud.
- Cisco Next-Generation Firewall / Firepower Threat Defense (Virtual Appliance):The Cisco Firepower NGFW helps you prevent breaches, get visibility to stop threats fast, and automate operations to save time. A next-generation firewall (NGFW) is a network security device that provides capabilities beyond a traditional, stateful firewall by adding capabilities like application visibility and control, Next-Generation IPS, URL filtering, and Advanced Malware Protection (AMP).
Cisco Anyconnect Windows 10 Download
Due to layer-2 abstraction in the cloud, it not possible to provide native firewall high availability, firewall clustering, and VPN clustering. AWS offers native services like AWS route53, AWS route tables that enable DNS based load balancing.
Traffic Flow:
- The remote access VPN user initiates a VPN connection using a hostname (example: answamivpn.com), and the DNS server returns an IP address. AWS route53 monitors all the firewalls using AWS route53 health checks
- Remote user makes the connection to the firewall
- Access the resources hosted in AWS
Recommendation for the architecture shown in figure 2:
- Each availability zone (AZ) should have multiple firewalls (ASAv or NGFWv)
- Each firewall should have a dedicated VPN pool (i.e. separate VPN pool for each firewall)
- VPN pool should be outside of VPC CIDR range, avoid overlapping networks
- Control traffic using AWS route table
- Enable weighted average load balancing on AWS route53
- AWS route53 should track firewalls public IP/elastic IP using port 443
- Cisco Duo: Multi-factor authentication
- Cisco Umbrella Roaming Security Module: DNS layer security and IP enforcement
- Cisco AMP enabler: File and Malware analysis
- Cisco ISE: Authentication and Posture
- SWC: Visibility
The architecture shown in figure 2, is a scalable and resilient design for a single VPC deployment. This architecture is based on the principle of a distributed architecture. In the case of a multiple VPN architecture, we recommend deploying bigger firewall instances (example: C5.2xl 0r C5.4xl) in a centralized VPC.
In the case of a multi-vpc architecture, we recommend deploying multiple instances of bigger firewalls in a centralized VPC (known as security-hub VPC) and the connect security-hub VPC to spoke VPCs using AWS Transit Gateway.
The AWS transit gateway can have the following types of attachments:
- VPC attachment (used for VPC and AWS Direct Connect (DX) connection)
- VPN attachment (used for IPsec connectivity to DC)
- Peering connection (used for peering two AWS transit gateway – not shown in this architecture)
Traffic Flow:
- The remote access VPN user initiates a VPN connection using a hostname (example: answamivpn.com), and the DNS server returns an IP address. AWS route53 monitors all the firewalls using AWS route53 health checks.
- Remote user makes the connection to the firewall.
- Access the resources hosted in AWS.
Recommendation for the architecture shown in figure 3:
- Each availability zone (AZ) should have multiple firewalls (ASAv or NGFWv)
- Each firewall should have a dedicated VPN pool (i.e. separate VPN pool for each firewall)
- VPN pool should be outside of VPC CIDR range, avoid overlapping networks
- Control traffic using AWS route table
- Enable weighted average load balancing on AWS route53
- Use AWS Transit Gateway for interconnecting VPC
- For a hybrid cloud architecture, terminate VPN on the firewalls at the edge in the secure hub vpc or use VPN attachment on the AWS transit gateway.
- AWS route53 should track firewalls public IP/elastic IP using port 443
- Cisco Duo: Multi-factor authentication
- Cisco Umbrella Roaming Security Module: DNS layer security and IP enforcement
- Cisco AMP enabler: File and Malware analysis
- Cisco ISE: Authentication and Posture
- SWC: Visibility
Detailed information on the architecture described in figure3 is available this video: https://www.youtube.com/watch?v=ReI6I0eWyKc
In addition to the above information, we recommend checking out our Cisco Secure Remote Worker design guide that addresses a specific use case of remote access VPN connection covered in the SAFE Internet Edge Architecture Guide. The design for remote access VPN connections includes the Cisco AnyConnect Secure Mobility Client, Cisco Duo, Cisco Umbrella, and Cisco Advanced Malware Protection (AMP) for Endpoints.
Design Guide: https://www.cisco.com/c/dam/en/us/solutions/collateral/enterprise/design-zone-mobility/secure-remoteDe-worker-design-guide.pdf
Thanks,
Anubhav Swami (CCIEx2: 21208)
Security Solutions Architect
Cisco Systems Inc.
Cisco Blog: https://blogs.cisco.com/author/anubhavswami
YouTube Channel: https://www.youtube.com/anubhavswami
Reference links:
Cisco SAFE design guide for AWS: https://www.cisco.com/c/dam/en/us/solutions/collateral/enterprise/design-zone-security/secure-aws-design.pdf
Cisco SAFE Cloud Architecture Guide: https://www.cisco.com/c/dam/en/us/solutions/collateral/design-zone/cisco-validated-profiles/safe-secure-cloud-architecture-guide.pdf
Cisco SAFE secure remote worker: https://www.cisco.com/c/dam/en/us/solutions/collateral/enterprise/design-zone-mobility/secure-remote-worker-design-guide.pdf
Cisco Stealthwatch Cloud: https://www.cisco.com/c/en/us/products/security/stealthwatch-cloud/index.html
Cisco AMP for Endpoints: https://www.cisco.com/c/en/us/products/security/amp-for-endpoints/index.html
Cisco Duo: https://duo.com/
Cisco Umbrella: https://umbrella.cisco.com/
Cisco ASA: https://www.cisco.com/c/en/us/products/security/asa-firepower-services/index.html
Cisco Next-Generation Firewall: https://www.cisco.com/c/en/us/products/security/firewalls/index.html
Amazon Web Service: https://aws.amazon.com/
Amazon Load Balancer: https://aws.amazon.com/elasticloadbalancing/
Amazon Route53: https://aws.amazon.com/route53/
Amazon Route Table: https://docs.aws.amazon.com/vpc/latest/userguide/VPC_Route_Tables.html
Amazon Transit Gateway: https://aws.amazon.com/transit-gateway/
Cisco Live Sessions:
NGFWv and ASAv in AWS and Azure (BRKSEC-2064): https://www.ciscolive.com/global/on-demand-library.html?search=Anubhav%20Swami#/session/1542224327848001r3qI
Deploy ASAv and NGFWv in AWS and Azure (LTRSEC-3052): https://www.ciscolive.com/global/on-demand-library.html?search=Anubhav%20Swami#/session/1564527389250001ckvR
ARM yourself using NGFWv and ASAv in Azure (BRKSEC-3093): https://www.ciscolive.com/global/on-demand-library.html?search=Anubhav%20Swami#/session/1560880389440001ntSs
YouTube Videos:
YouTube Channel: https://www.youtube.com/anubhavswami
Cisco Anyconnect Arch Linux
Cisco Anyconnect Arch For Windows
